introduction: balancing complaint resistance and legal compliance
in an environment where both supervision and user trust are of equal importance, the anti-complaint hong kong vps hosting ban defense capability involves not only resisting malicious or abusive complaints, but also protecting normal business continuity under the premise of legal compliance. this article analyzes how host providers can reduce mis-blocking, shorten recovery time, and improve overall availability from three dimensions: network architecture, operational processes, and technical means.
network layer protection and isolation strategy
the network layer is the first line of defense against scoping bans. the use of virtualized network isolation, vlan/vrf segmentation, independent ip pools and rate limiting strategies can reduce the risk of "simultaneity"; in addition, combined with ddos cleaning, traffic threshold detection and the support of upstream routing partners, it can quickly cut peaks and maintain normal user access when encountering large-scale complaints or traffic anomalies.
ip and routing management to combat false blocking
reasonable ip management and routing relationships directly affect the recovery speed after being banned. cooperation between operators and upstream isps, bgp route redundancy and backup ip segment preparation can speed up switching; while maintaining good reverse dns, ptr records and ip reputation monitoring can reduce automatic bans triggered by insufficient trust.
ip rotation and backup mechanism
within the scope of legal compliance, providing a stable ip replacement and migration process can reduce the impact of single-point complaints. automated migration scripts, snapshot system deployment and configuration management can allow affected instances to recover faster, but must be coupled with strict customer review and abuse prevention to prevent them from being used to circumvent law enforcement or policies.
monitoring, logging and evidence preservation
complete monitoring and logging are at the core of responding to complaints and grievances. through centralized logs, syslog/elk links, traffic records and behavioral audits, verifiable evidence can be provided for complaints; at the same time, automatic alarms, anomaly detection and correlation analysis can also identify potential risks and trigger mitigation strategies before complaints erupt.
operations and compliance processes: rapid response and transparent communication
technical means need to be matched with clear operational processes. establishing a professional abuse handling team, standardized complaint review and appeal channels, and a liaison mechanism with law enforcement agencies can strive for faster review and recovery within the legal and reasonable scope, and avoid long-term business unavailability due to slow processes.
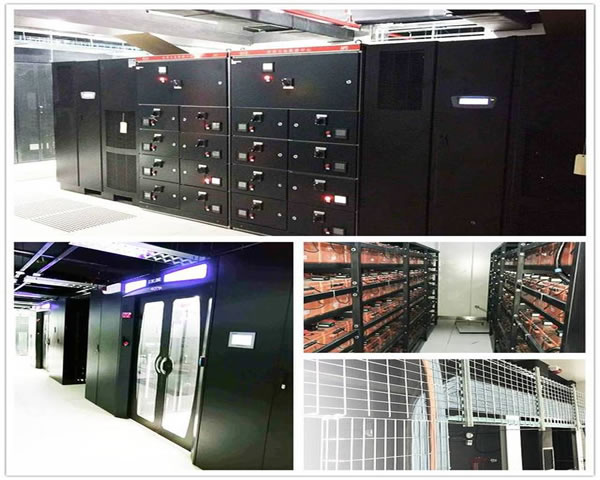
resource isolation and virtualization guarantee
through isolation measures such as containerization, independent virtual machines, and resource quotas, the behavior of a single tenant can be restricted from affecting its neighbors, thereby reducing the risk of the entire physical unit being affected due to the blocking of one server. hardware isolation and on-demand elastic expansion also help to quickly migrate workloads when complaints or attacks occur.
automated recovery and backup strategies
regular snapshots, offline backups and automated recovery processes are key to maintaining business continuity. combined with configuration management tools and basic image libraries, services can be quickly rebuilt in a healthy environment after the affected instance is taken offline, while original traces are retained for appeals and audits.
summary and suggestions
anti-complaint the ban defense capability of hong kong vps hosting is a collaborative product of technology, operations and compliance. it is recommended to select a service provider with network redundancy, good upstream relationships, and complete log and abuse processes, deploy resource isolation and automated recovery mechanisms, and conduct reputation management and compliance audits in daily operations to maximize business availability and resistance to mis-blocking within the legal scope.
- Latest articles
- A Comprehensive Analysis of the Risks and Optimization Strategies for Enterprises Moving to Alibaba Cloud Hong Kong CN2
- interpretation of key indicators of vietnam cloud server data analysis and operation optimization roadmap
- a complete guide to japan’s native ip node purchase channels and price/performance comparison
- low-latency optimization strategy for cloud servers in southeast asia and cambodia in the edge computing era
- comparison of the latest price trends and price/performance evaluation of japanese cloud servers
- common troubleshooting and processing procedures in malaysia cn2 network environment
- comparative study on compliance, backup and security of vietnamese cn2 service providers
- availability zone selection and latency monitoring essential checklist for cloud server operation and maintenance in the eastern united states
- troubleshooting: quick diagnosis and solutions to common connection problems with vietnam vps ladders
- Popular tags
-
Experience the free one-month activities and benefits of hong kong cloud servers
learn about the free experience activities and advantages of hong kong cloud servers to help you choose the most suitable cloud service. -
Tencent Cloud Hong Kong server delay compared with other brands' performance
This article analyzes the delay performance of Tencent Cloud Hong Kong server in detail and compares it with other brands of servers to help users choose the right server. -
Sharing of configuration and management skills of Hong Kong VPS site group
This article shares the configuration and management skills of Hong Kong VPS site groups, including how to choose the right server, optimize performance, etc.


